Verifying...
The UX Nobody Draws in the Wireframe
The UX Nobody Draws in the Wireframe
Online-to-Offline Event Payment Design Payment design isn't about the button. It's about everything the button sets in motion.


Here's a question I don't see asked enough:
Where does UX end?
The standard answer is somewhere around the last screen — confirmation page, receipt email, maybe a follow-up notification. The job is done. The user is happy. The designer moves on.
But I want to argue that answer is wrong. And payment flows are the best place to prove it.
The screen is a lie detector
When a user reaches a checkout page, something shifts. They're no longer evaluating your product — they're evaluating you. The mental question isn't "do I want this?" anymore. It's "do I trust this enough to type in my card number?"
Most UX responses to this are cosmetic: brand color on the button, reassuring microcopy, a padlock icon. These things matter at the margin. But they're treating a systemic problem with surface-level solutions.
The real sources of trust in a payment flow are almost entirely invisible.
A Stripe Buy Button that opens a Modal instead of redirecting to an iframe isn't just a technical choice — it's a UX choice. The user never consciously notices the difference. But their browser does, Stripe's fraud systems do, and somewhere in the stack, the absence of a cross-origin frame removes an entire category of risk. Trust isn't always felt. Sometimes it's just the absence of the wrong thing happening.
The checkbox that meant something

The event required users to confirm a legal document before paying. I could have put the terms link inside Stripe's native "custom text" field — one line, one tick, done. Compliant. Forgettable.
Instead, I built a gate. The Buy Button doesn't exist until the checkbox is checked. No tricks, no gray-out, no tooltip. The button is simply not there.
This is friction by design. And UX orthodoxy will tell you friction is the enemy. But that's a shallow reading of what friction does. In certain moments — legal commitment, irreversible action, financial transaction — friction is the experience. The slight resistance is the system communicating: this counts.
The question UX should be asking isn't "how do we remove friction?" It's "which friction is load-bearing?"
Webhooks are UX infrastructure
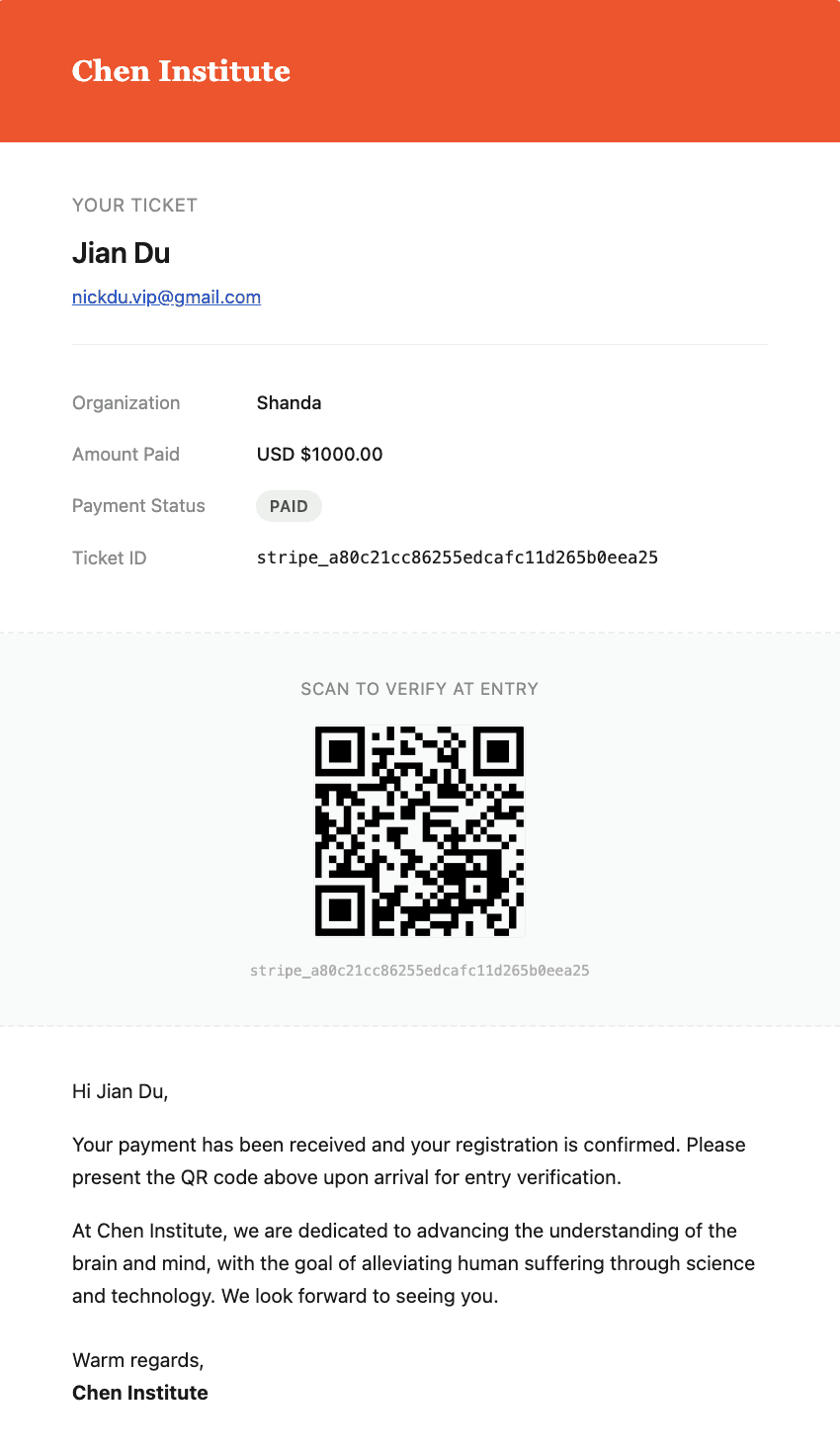
After a successful payment, a checkout.session.completed event fires from Stripe to n8n. Two fields get extracted: email and name. Three nodes total.
This is usually called backend work. I want to call it something else: the moment the system learns the user exists.
Everything downstream — the welcome message, the CRM record, the membership activation — depends on this pipeline running cleanly. If it breaks, the user paid and received nothing. No error screen. No feedback. Just silence. From a UX perspective, that silence is the worst possible outcome. Worse than a failed payment, because at least a failed payment tells you something.
The Webhook pipeline isn't plumbing. It's the nervous system of the post-payment experience. Its reliability is UX.
Online payment, offline identity
Here's where I think most payment UX thinking stops too early.
For an online-to-offline event, payment is not the end of the journey. It's the beginning of an identity claim. The attendee who paid online will show up at a physical venue and expect to be recognized — instantly, correctly, without friction.
That recognition is only possible if you've designed what happens to every single checkout.session.completed event — not just the clean ones.
This is where most payment UX thinking stops at the wrong layer. Storing a record in PostgreSQL is the easy part. The harder design question is: what is the intended fate of each event, and have you designed for all of them?
A normal event: payment confirmed, livemode: true, email present, name present — write to the CRM, activate access, queue the welcome message. Straightforward.
An abnormal event: webhook fires twice for the same session due to a network retry. Does your pipeline write two records? Does the attendee get checked in twice? Does a second badge print at the door? If you haven't designed this path, the system will answer for you — and it usually answers badly.
An illegal event: a replayed webhook, a tampered payload, a livemode: false event that somehow reached your production endpoint. Does your system catch it? Does it log it, alert on it, discard it silently? Each of these is a different UX outcome for a real person downstream.
Crossing the security experience chasm means treating every event as a design object — with a defined origin, a verified signature, a mapped destination, and a documented failure mode. The PostgreSQL schema is not the destination. It's the proof that every upstream decision was made on purpose.
This is the full UX arc nobody draws in the wireframe: not just what happens when everything goes right, but who designed what happens when it doesn't.
The user walking up to the desk doesn't know any of this. They just know their name was called correctly. That feeling — of being expected, of the system knowing exactly who they are — is the residue of a hundred invisible decisions made in the right order.
A harder definition of UX
I'm not arguing that interface design doesn't matter. It does. But I think we've allowed "UX" to become a synonym for "what the user sees," and that boundary is making our work smaller than it should be.
In a payment context, UX is:
The architectural decision that keeps card data off your server
The webhook pipeline that fires within 200ms of a transaction
The database schema that makes offline verification instantaneous
The legal gate that turns a checkbox into a commitment
The brand color on the button (yes, this too — but last, not first)
The best payment experience isn't one where everything looks right. It's one where everything is right — and the user only ever notices the surface, because everything underneath held.
That's the design work worth doing.